Realtor.com operator Move Inc. says it received a ransom demand in conjunction with a “distributed denial of service” cyberattack that has disrupted realtor.com and other Move Inc. websites for two days running, and which could take several more days to fully resolve.
Move said it did not respond to the ransom demand, and is working with its network service providers and Internet security experts including the Prolexic division of Akamai Technologies Inc. to mitigate the attack and restore operations. On Thursday night, realtor.com appeared to be functioning, while Top Producer was still affected by the “DDoS” attack.
Move said it’s migrating its Internet services to a different network architecture — a complex plan that “will take several days to complete.”
The distributed denial of service attack “is driving massive amounts of traffic from external sources to Move’s data center, making realtor.com, Top Producer services and Move’s other Internet services available intermittently,” the company said. The attacks have also “targeted and impacted the redundant aspects” of Move’s systems.
Federal law enforcement officials are working to determine the attack’s origin, Move said.
Unlike a precisely executed hack job, cyberattackers employing a distributed denial of service attack assault websites with massive amounts of “zombie traffic,” which can bog them down and ultimately flatten them. It’s an attack by broad sword, and it’s on the rise.
According to security firm Arbor Networks, the number of distributed denial of service attacks larger than 20 gigabytes per second increased by eightfold from 2012 to 2013, Forbes reports, and continues to rise.
Although the average DDoS attack is still in the 1 to 5 GB per second range, some recent attacks have measured up to 300 GB per second, enough to flatten a corporate network, Forbes noted.
Other recent victims of distributed denial of service attacks include Evernote, Twitter’s popular messaging app TweetDeck, RSS reader Feedly, video site Vimeo, project management platform Basecamp, and inbound marketing tech firm Moz.
According to a scan conducted by Arbor Networks for Inman News, the following Move sites were not affected by the attack: Doorsteps.com, Moving.com, HomeInsight.com, SeniorHousingNet.com, HomeFair.com, Relocation.com, ListHub.com and TigerLead.com.
The scan did not reveal what country the attack originated from.
Questions still outstanding:
- How big was the attack in terms of gigabytes per second?
- Did the attack occur at the network, domain name server, application or another level?
- Why did it take so long to recover? Was this a sophisticated attack? In what way?
- Had Move taken steps to prevent a distributed denial of service attack, either internally or through a vendor like Arbor Networks, Prolexic or Cloudflare?
- What will be done to mitigate further attacks?
Move says it’s “consulting with appropriate federal law enforcement officials and other technology companies that have been targets of DDoS attacks in recent months to review best practices for responding.”
Distributed denial of service attacks have been around for years, said Dan Holden, director of the security engineering response team at Arbor Networks.
Unlike simpler (undistributed) denial of service attacks, which generate traffic from a single source, distributed denial of service attacks involve two or more “botnets.” In a distributed attack, a botnet computer or server co-opts other computers and servers to direct traffic to specific sites. It’s a coordinated series of attacks, Holden said.
Holden compared the botnet-controlled computers and servers in a distributed denial of service attack event to zombies.
There are a number of reasons why such attacks are on the rise, Holden said. First of all, it’s a relatively cheap and easy cyberattack to coordinate, he said. In addition, more hackers have learned how to use techniques like amplifying and replicating traffic to create larger distributed attacks, he said.
According to a scan Arbor Networks conducted for Inman News, the first distributed denial of service attack hit realtor.com at 4:58 p.m. Eastern time Tuesday. A series of other attacks occurred shortly after, some at the same time, the scan revealed.
Move brought in Arbor Networks competitor Prolexic on Tuesday soon after it learned of the attack, said Robert Morten, director of public relations for Akamai Technologies, which owns Prolexic. Since then, Prolexic has been working to help Move get its affected sites back up and running.
Real estate portals are not typically a high-priority target for distributed denial of service attacks, said David Fernandez, head of Prolexic’s security engineering and response team, who’s been helping Move with its attack.
The are three primary motives for DDoS attacks, Fernandez said. They are conducted to:
- Gain a competitive advantage over a competitor.
- Extort a company, forcing them to pay up or risk a a distributed attack.
- Make a political point or advocate for a cause as in hacker activism, “hacktivism.”
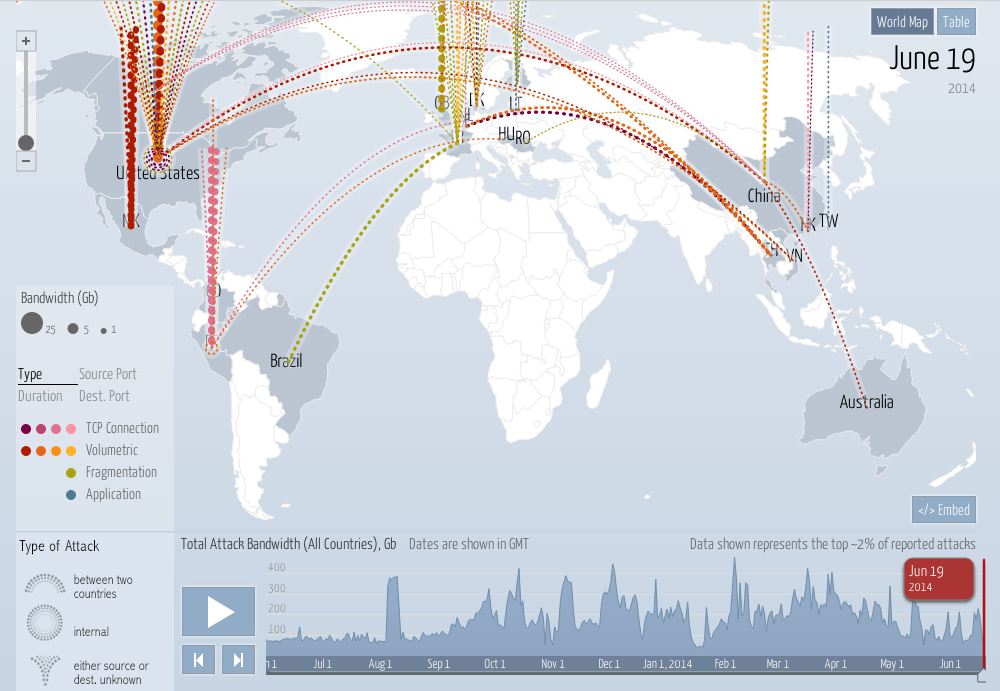
Arbor Networks maintains a website that shows distributed denial of service attacks by country of origin in real time.
According to Forbes, other security experts say distributed attacks are often a diversionary tactic used by thieves who are after credit card numbers or other sensitive data.
Move said it had no evidence that the attack “includes or has resulted in any compromise of data or other content on its websites.”
Holden characterized the attack on Move’s websites as serious. “To put together an attack like this for this long, someone has to care,” he said. “The motivation is serious.”
A distributed attack “is not a complex action to take,” Holden said. “The complexities lie in the motivation (of whomever coordinated the attack).”
Move has defended itself from DDoS attacks before, but this week’s attack was large enough that it had to bring in Prolexic, the company said in a statement.
Both Holden and Fernandez say it’s becoming standard practice for firms to engage their companies as insurance against distributed denial of service attacks as they become larger and more common.







